Welcome back to Linux Command Line Hackery series, I hope you've enjoyed this series so far and would have learned something (at least a bit). Today we're going to get into user management, that is we are going to learn commands that will help us add and remove users and groups. So bring it on...
Before we get into adding new users to our system lets first talk about a command that will be useful if you are a non-root user.
Command: sudo
Syntax: sudo [options] command
Description: sudo allows a permitted user to execute a command as a superuser or another user.
Since the commands to follow need root privileges, if you are not root then don't forget to prefix these commands with sudo command. And yes you'll need to enter the root password in order to execute any command with sudo as root.
Command: useradd
Syntax: useradd [options] username
Description: this command is used for creating new user but is kinda old school.
Lets try to add a new user to our box.
[Note: I'm performing these commands as root user, you'll need root privileges to add a new user to your box. If you aren't root then you can try these commands by prefixing the sudo command at the very beginning of these command like this sudo useradd joe. You'll be prompted for your root password, enter it and you're good to go]
useradd joe
To verify that this command has really added a user to our box we can look at three files that store a users data on a Linux box, which are:
/etc/passwd -> this file stores information about a user separated by colons in this manner, first is login name, then in past there used to be an encrypted password hash at the second place however since the password hashes were moved to shadow file now it has a cross (x) there, then there is user id, after it is the user's group id, following it is a comment field, then the next field contains users home directory, and at last is the login shell of the user.
/etc/group -> this file stores information about groups, that is id of the group and to which group an user belongs.
/etc/shadow -> this file stores the encrypted password of users.
Using our command line techniques we learned so far lets check out these files and verify if our user has been created:
cat /etc/passwd /etc/group /etc/shadow | grep joe

In the above screenshot you can notice an ! in the /etc/shadow, this means the password of this user has not been set yet. That means we have to set the password of user joe manually, lets do just that.
Command: passwd
Syntax: passwd [options] [username]
Description: this command is used to change the password of user accounts.
Note that this command needs root privileges. So if you are not root then prefix this command with sudo.
passwd joe

After typing this command, you'll be prompted password and then for verifying your password. The password won't show up on the terminal.
Now joe's account is up and running with a password.
The useradd command is a old school command, lets create a new user with a different command which is kinda interactive.
Command: adduser
Syntax: adduser [options] user
Description: adduser command adds a user to the system. It is more friendly front-end to the useradd command.
So lets create a new user with adduser.
adduser jane

as seen in the image it prompts for password, full name and many other things and thus is easy to use.
OK now we know how to create a user its time to create a group which is very easy.
Command: addgroup
Syntax: addgroup [options] groupname
Description: This command is used to create a new group or add an existing user to an existing group.
We create a new group like this
addgroup grownups

So now we have a group called grownups, you can verify it by looking at /etc/group file.
Since joe is not a grownup user yet but jane is we'll add jane to grownups group like this:
addgroup jane grownups
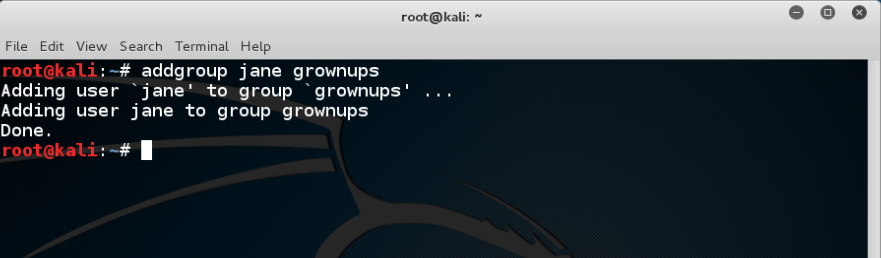
Now jane is the member of grownups.
Its time to learn how to remove a user from our system and how to remove a group from the system, lets get straight to that.
Command: deluser
Syntax: deluser [options] username
Description: remove a user from system.
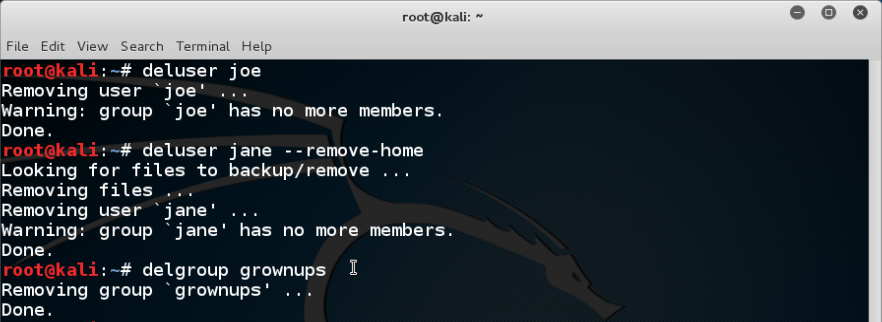
Lets remove joe from our system
deluser joe
Yes its as easy as that. But remember by default deluser will remove the user without removing the home directory or any other files owned by the user. Removing the home directory can be achieved by using the --remove-home option.
deluser jane --remove-home
Also the --remove-all-files option removes all the files from the system owned by the user (better watch-out). And to create a backup of all the files before deleting use the --backup option.
We don't need grownups group so lets remove it.
Command: delgroup
Syntax: delgroup [options] groupname
Description: remove a group from the system.
To remove grownups group just type:
delgroup grownups
That's it for today hope you got something in your head.
- Hacking Tools Software
- Github Hacking Tools
- Free Pentest Tools For Windows
- Pentest Tools For Android
- Hackrf Tools
- Pentest Tools Website
- Pentest Tools Bluekeep
- Hack Tool Apk
- Hacking Tools Windows 10
- Pentest Tools For Ubuntu
- Pentest Tools Github
- Hak5 Tools
- World No 1 Hacker Software
- Hacking Tools Download
- How To Install Pentest Tools In Ubuntu
- Hacking Tools For Windows Free Download
- Hacker Tools For Windows
- World No 1 Hacker Software
- Hacking Tools Online
- Hacker Tools For Mac
- Hacker Tools List
- Github Hacking Tools
- Hacking Tools Mac
- Hack Rom Tools
- Hacking App
- Nsa Hack Tools
- Android Hack Tools Github
- Pentest Tools Website
- Hacker Tools Linux
- Pentest Tools Github
- Hacker Techniques Tools And Incident Handling
- Hacker Tools Apk
- Hacking Tools Kit
- Pentest Tools For Ubuntu
- Hack Tools For Games
- Github Hacking Tools
- Hacker Tools 2020
- Hacker Tools Apk Download
- Termux Hacking Tools 2019
- Hack Tools Github
- Hack Website Online Tool
- Hacker Tools 2019
- Nsa Hacker Tools
- What Are Hacking Tools
- Pentest Box Tools Download
- How To Hack
- Hacking Tools Pc
- Easy Hack Tools
- Hacking Tools Mac
- Pentest Tools Github
- Pentest Tools Port Scanner
- New Hacker Tools
- Pentest Tools List
- Pentest Tools Nmap
- Hack Tools Github
- Hackers Toolbox
- Hacking Tools For Windows Free Download
- Hackrf Tools
- Hack Tools For Mac
- Pentest Tools For Windows
- Github Hacking Tools
- Beginner Hacker Tools
- Kik Hack Tools
- Usb Pentest Tools
- Beginner Hacker Tools
- Hacking Tools Github
- Physical Pentest Tools
- Pentest Tools
- Tools 4 Hack
- New Hacker Tools
- Hacker Hardware Tools
- Hack Tools Pc
- Hacking Tools Software
- Termux Hacking Tools 2019
- Pentest Tools Website
- Pentest Automation Tools
- Hacking Tools For Windows 7
- Hacking Tools Mac
- Hak5 Tools
- Hacker Tools Apk
- Termux Hacking Tools 2019
- Hacking Tools Software
- Hacker Tools Github
- Pentest Tools Url Fuzzer
- Hacker Tools Free
- Bluetooth Hacking Tools Kali
- Hacker Tools Apk Download
- Install Pentest Tools Ubuntu
- Hackers Toolbox
- Pentest Tools Github
- Pentest Tools Website Vulnerability
- Pentest Reporting Tools
- Hacker Tools 2019
- Hacking Tools For Beginners
- Hack Tools For Pc
- Hacks And Tools
- Hacking Tools For Mac
- Physical Pentest Tools
- Hacker Tools Apk
- Pentest Tools Subdomain
- Hacking Tools For Windows
- Game Hacking
- Pentest Tools For Mac
- Pentest Tools List
- Hack Tool Apk No Root
- Nsa Hack Tools Download
- Hacking Tools For Beginners
- Hacking Tools For Pc
- What Are Hacking Tools
- Hacker Tools Software
- Hack And Tools
- Pentest Tools Bluekeep
- Termux Hacking Tools 2019
- Usb Pentest Tools
- Pentest Tools Free
- Pentest Recon Tools
- Hacking Tools Name


No hay comentarios:
Publicar un comentario